Post not found
Similar Posts

Anatomy of an Unknown AMOS Stealer: From Alert to Immunity in Hours
A previously undocumented AMOS stealer variant compromised a macOS endpoint. No known hashes, no C2 data in any public database. ...

Why Edge Should Be Your Only Corporate Browser
The browser nobody satisfies chose became the one everybody manages. Most companies never made a deliberate decision for Chrome; it ...

No Malware Needed. Just One Admin Account.
On March 11, 2026, Handala wiped devices across 79 countries using nothing but a compromised Intune admin account. No malware, ...

Six Agents. Four Weeks. Real Production.
Six companies, four weeks of building, six working AI agents — that was the first glueckkanja AI Agent Hackathon. Kiekert, ...

Exchange AD Split Permissions without regrets
Even organizations that have fully migrated their mailboxes to the cloud often still run on-premises Exchange servers and with them, ...

AuthCodeFix aka ConsentFix
Just before year's end, ConsentFix emerges: a clever OAuth-based attack that abuses legitimate authentication flows to steal the authorization code, ...

Our Application Process Explained
You've discovered an exciting position with us and want to apply? Great – we're always happy to welcome new talent! ...

Cloud-first at the airport: Microsoft Partner of the Year Awards 2025
Out of more than 4,600 nominations from over 100 countries, one project stood out as a showcase of what modern ...

Preventing Cyber Attacks: How Companies Build Resilience with IT Structures
Saturday morning, somewhere in Germany. While the weekend is just beginning for many, our team notices the first warning signs ...
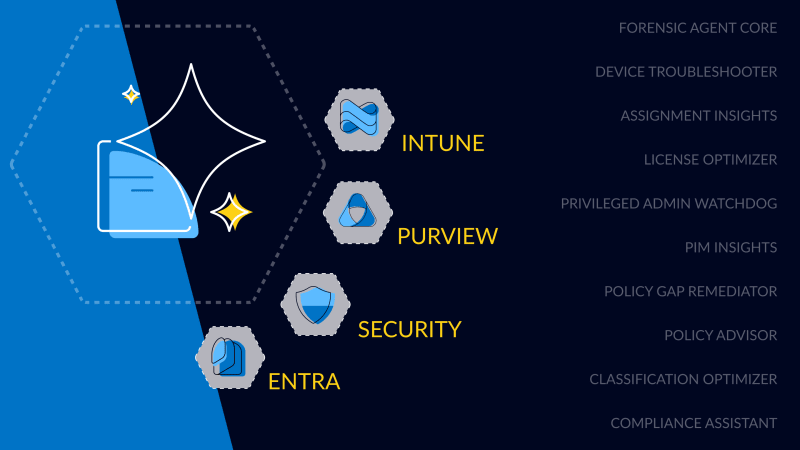
First Worldwide: glueckkanja Security Copilot Agents
glueckkanja is among the first partners in the Microsoft Security Store Preview, delivering 10 Microsoft-native Security Copilot Agents across Security, ...

Global Secure Access Unlocked
This blog explores how Microsoft Global Secure Access enhances security and control in our Managed Red Tenant. With Entra Internet ...

This is why you need a solid infrastructure to be agent-ready in 2025
Before Microsoft 365 Copilot Agents can deliver real value, the foundation must be solid: clean data, proper permissions, and a ...

Monitoring That Grows With You – Organic Solutions in Azure
How modern Azure monitoring creates transparency and leaves room for what matters most

Next Level Azure IaC: Azure Verified Modules
Infrastructure-as-Code (IaC), especially with Terraform, is a key component of our Azure Foundation and a fundamental element of every cloud ...

Inside Akira Stealer: A full technical analysis of a modular stealer
It started with a single Defender alert in Microsoft 365. No malware, no signatures, no panic. Just a whisper in ...
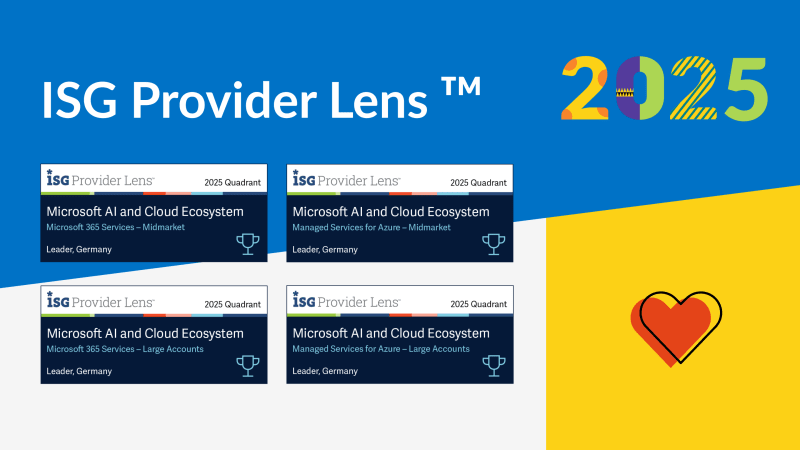
Four in a row. glueckkanja once again a Leader in ISG
The ISG Provider Lens™ 2025 study once again recognizes glueckkanja as a Leader in both Managed Services for Azure and ...
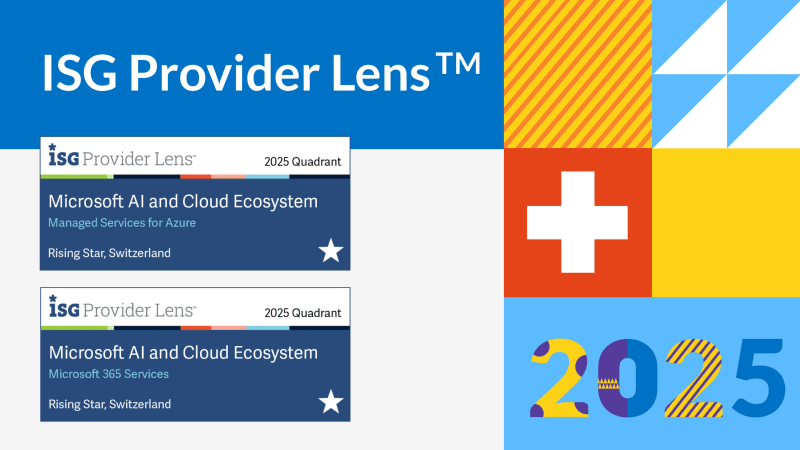
Switzerland steps up. glueckkanja becomes ISG Rising Star
glueckkanja Switzerland has been named a 'Rising Star' by ISG in the categories Microsoft 365 Services and Managed Services for ...

glueckkanja remains among the Top 5 MSSPs worldwide
The Microsoft Security Excellence Awards are among the most prestigious honors in the industry. At RSA Conference 2025 in San ...

Hello Clöud
Austrian companies are currently at a turning point. Digitalization is accelerating rapidly. At the same time, the demands on IT ...

'23, '24, '25 – the triple is complete!
glueckkanja is once again a finalist at the Security MSSP of the Year Awards, placing us among the world's leading ...

Compliant Device Bypass - All you need to know!
In this blog post, glueckkanja's MVP Fabian Bader, Chris Brumm and Thomas Naunheim gather details about the Compliant Device Bypass ...

